Focus Features

Full Outsourced Service

Around-the-clock Monitoring and Operation

Multi-Layer Defense
1.Fully Outsourcing Firewall Operations

We offer a one-stop service including procurement, initial settings, installation,and operation of firewalls, which frees you from the burden of firewall management. We leverage the operational know-how we have fostered through the operation of over 2,000 devices in Japan to provide highly reliable service in the ASEAN area.
2.Around-the-clock Monitoring and Operation by Expert Engineers
Our security expert engineers remotely monitor your firewalls 24 × 7. When disconnection or abnormality is detected, we will contact you and perform recovery. Flexible support such as firmware version upgrades and on-site support is also available.
3.Boost Your Network Security with Multiple Layers of Defenses

Supports hardware and virtual appliances of Palo Alto Networks and Fortigate. In addition to detecting and defending against known threats, the service detects and defends against unknown threats with sandbox. We provide the equipment and licenses, or you can use your existing assets to deploy the latest security measures with minimal investment.
Service Features
Variety of security functions which meet your needs
Monitoring / Maintenance
We monitor your firewall device 24 × 7 from monitoring systems. In the event of an incident, we will notify you and support restoration as soon as possible.
Anomaly Detection
Our proprietary anomaly detection systems will learn your communication trends and detect anomalies.
Items that can be viewed in an on-box report
- Number of allowed connections
- Number of rejected connections
Examples of abnormality which our anomaly detection systems detected
- Virus infected PCs that communicate abnormally.
- Sudden increase of communication to web servers in the DMZ.
Monthly report

A monthly report shows you a summary of the incident responses and the operating status of the firewall.
Variety of options
Optional features such as extended support, hot standby, malware protection, VPN, and others are ready for your further needs.
Supported Devices
You can choose the perfect appliance and virtual firewall device for your network environment and application, or you can also build your VM server on IIJ Group's cloud services.
Palo Alto PA Series / Palo Alto VM-Series

Next-generation firewalls that realize application-level identification and control. The threat prevention option, which combines IPS and anti-malware capabilities to block threats comprehensively, and WildFire option, which uses zero-day exploits and advanced evasion techniques to detect unknown malware are available.
FortiGate-VM / FortiGate Appliance

Next-generation NGFW/UTM (Unified Threat Management) firewall that combines multiple security functions in a single unit with high performance and excellent cost performance by the proprietary FortiASIC security processor.
Features of Palo Alto PA Series and Palo Alto VM-Series
Next-Generation Firewall for Multi-Level Defense with One Device
The Palo Alto Networks PA-Series provides the traditional signature to detect and protect against known threats, as well as the sandbox to detect and protect against unknown threats. Besides, it is possible to identify, visualize, and control applications that were not possible with conventional firewalls.
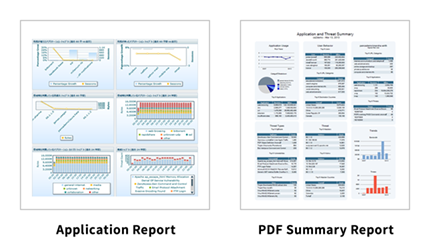
Visualize Communication and Usage by On-box Reports
You can specify a period for each category, such as applications or traffic, to select logs of information that you need and view them as reports. In addition to understanding the network status, this allows you to understand the activity status of each application or user.
Items that can be viewed in an on-box report
- Traffic logs
- Threat log
- System log
- Application aggregation report
- Threat protection report
On-Box Report Display Format
- Application report
- Threat report
- Traffic report
- PDF Summary report
-
* The reporting period you can refer to depends on the number of communication logs.
Feature Overview
- Threat Protection
-
Protects the system from known threats such as viruses, spyware, and vulnerability attacks.
Detect and Protect Communications by Threat Protection Options
The Anti-virus and anti-spyware feature detects and protects communications suspected of being viruses or spyware, and the anti-vulnerability feature detects attack suspected of targeting vulnerabilities.。Advantage of the UTM Function of the Next-generation Firewall
Using the UTM function of the conventional firewall may severely degrade performance. However, Palo Alto Networks' next-generation firewalls offer threat protection features that use the software architecture (single-pass method) to reduce performance degradation.
- WildFire (Sandbox)
-
Detects and protects against unknown threats in sandboxes that cannot be prevented by traditional measures such as anti-virus, IPS, and URL filtering.
Share Maximum Threat Information in Cloud-based Sandboxes
A sandbox in the cloud allows you to maximize the sharing of information about threats while minimizing the hardware requirements. The signatures to be distributed are also generated from files transferred from WildFire users worldwide. Quickly recognize and protect against unknown threats.Generate Anti-Threat Signature to Collaborate with Threat Protection
If it is determined to be malware, an anti-virus signature is automatically generated and delivered to your device within an hour. The delivered signature is reflected in the settings of the anti-virus, IPS signature, and URL filtering functions to detect and protect against the latest threats.Generate Forensic Reports
Administrators can view the file information, session information, and file runtime behavior results on the portal site. Also, the portal site provides detailed information about which users have been targeted and what applications have been utilized.
- Application Identification (App-ID)
-
Identify, visualize, and control applications regardless of the port, protocol, SSL encryption, or detection avoidance action. For example, an application using the same port can be identified, visualized, and controlled while port 80 is permitted.
- User Identification (User-ID)
-
By linking with Microsoft's Active Directory servers, you can identify who is using which applications. This allows you to set up, visualize, and control applications that are permitted and prohibited for each department or user.
Features of FortiGate Appliances/ FortiGate -VM
Variety of Security Functions for a Good Value of the Price
The Anti-Virus, Intrusion Protection, Web Filtering, and Email Filtering functions provided by the FortiGate series work in conjunction with FortiGuard services to ensure that security measures are consistently based on the most up-to-date threat information.
At Fortinet's six security centers worldwide, over 200 security experts monitor and analyze threats around the world 24/7. The threat information accumulated here provides the latest signatures for Fortinet's products as FortiGuard services.
Performance of Fortinet's FortiGate appliances
The FortiGate, which provides a variety of security features with an excellent value for money, has won the No. 1 UTM market share for 16 consecutive years since 2004.
Feature Overview
- Anti-Malware (Optional Feature)
-
In addition to Anti-Virus, Intrusion Protection, and Web Filtering, the Email Filtering function is provided centrally for multiple levels of defense.
-
* Anti-malware options include anti-virus, intrusion protection, web filtering, and Email filtering.

Anti-Malware
Detects and removes viruses and spyware from SMTP, POP3, FTPs, IMAP, HTTP, and IMs to prevent intrusions into the company.
Intrusion Protection
Provides intrusion prevention (IPS) function. Protect your network from attackers by providing network-level protection.
Web Filter
Prevents access to malicious sites such as spyware/malware drive-by download sites, spam URLs, and phishing.
Email Filters
Provides email filtering capabilities. Enhance email security by tagging emails that might be spam and alerting users. -
- Anti-Malware (Anti-Virus) (Optional Feature)
-
Detects and protects against viruses and spyware traversing the FortiGate based on virus-definition files delivered from FortiGuard.
Quick Pattern File Update with Push Delivery
Virus-definition files are distributed in real-time from FortiGuard to FortiGate around the world, based on the latest viruses, spyware, and other threats information. This makes it possible to detect and protect new threats every day around the world faster.
*The average number of daily notification is four, but the number varies depending on whether threat information is updated or not.Detection and Defense Based on Virus Behavior
In addition to the detection and protection based on the definition file, this service can protect against viruses that are not contained in the definition file by the heuristic analysis, which scans the program code of the virus code.
- Anti-Malware (Intrusion Protection) (Optional Feature)
-
In addition to known threats through signature matching, heuristic detection that shows the behavior of communications protects the server and clients from unknown threats.
-
*This function is included in the anti-malware option.
Rich Signatures Based on Threat Information
The FortiGate maintains a rich IPS signature that exceeds 8000 (*) categorized by severity, target (server/client)/OS type, etc. They are kept up-to-date with information that is periodically delivered from the FortiGuard. This enables detection and defense against new attacks that occur daily around the world.
(*) Number of signatures as of end December 2015Detection and Defense Based on Communication Behavior
In conjunction with signature matching, heuristic detection protects against threats for which signatures have not been developed, based on communication behavior. -
- Anti-Malware (Web Filter) (Optional Feature)
-
The Fortigate connect to the FortiGuard in real-time to prevent spyware/malware drive-by-download sites, spam URLs, phishing, and other dangerous sites from being accessed.
Access Protection Based on Dangerous Website Information
When FortiGate detects web access, it communicates with FortiGuard for the URL or IP address information in real-time (*) and prevents access to malicious sites based on the results. Though the server location of malicious sites will be changed frequently, real-time queries can block access to those malicious sites with higher accuracy.
(*) Query results are cached for 60 minutes.-
* This feature is included in the anti-malware option.
-